This Content Is Only For Subscribers
A remote code execution vulnerability exists in the Credential Security Support Provider protocol (CredSSP). An attacker who successfully exploited this vulnerability could relay user credentials and use them to execute code on the target system.
CredSSP is an authentication provider which processes authentication requests for other applications; any application which depends on CredSSP for authentication may be vulnerable to this type of attack.
As an example of how an attacker could exploit this vulnerability against Remote Desktop Protocol, the attacker would need to run a specially crafted application and perform a man-in-the-middle attack against a Remote Desktop Protocol session. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
The security update addresses the vulnerability by correcting how Credential Security Support Provider protocol (CredSSP) validates requests during the authentication process.
1. SCENARIO
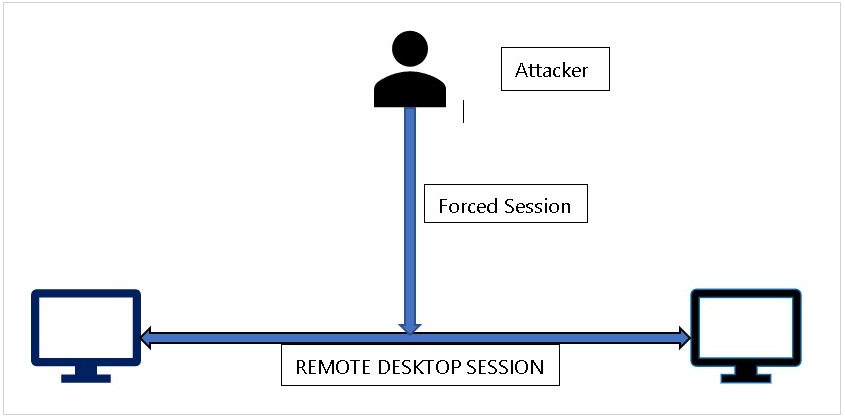
2. RDP SESSION
An update released by Microsoft (KB 4093492)on May 8, 2018, for Windows 10 Operation System was targeted to change the default settings CredSSP from Vulnerable to Mitigated.
A full list of the update and patches for all platform can be obtained from here.
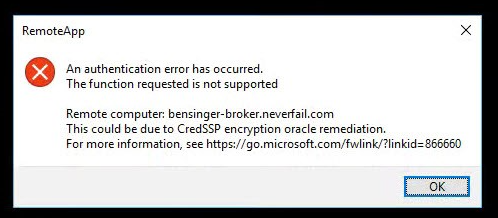
However, post patching this caused an issue where the patched clients were blocked from communicating with unpatched servers over RDP protocols.
This has been reported to cause an error thrown by Windows RDP as below:
3. WORKAROUND
Use the group policy settings changes described below to rollback the changes to ‘Vulnerable’ state to allow RDP access.
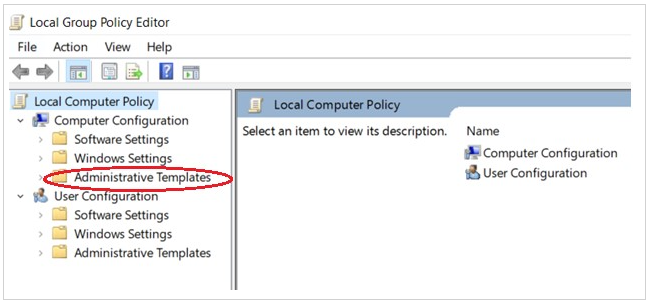
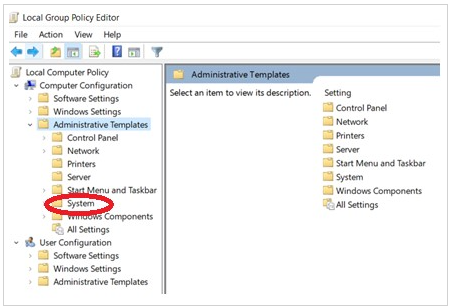
1. Open Group Policy Editor, by executing gpedit.msc
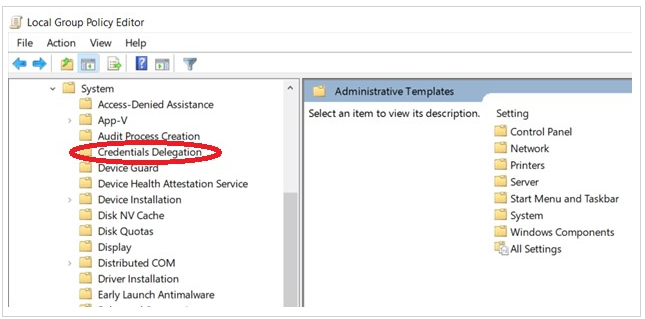
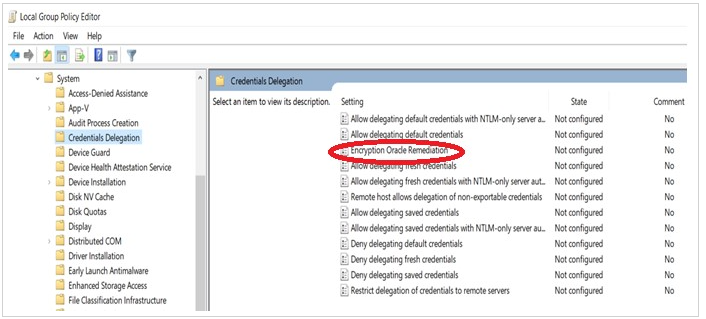
2. Policy path: Computer Configuration -> Administrative Templates -> System -> Credentials Delegation
Run gpedit.msc and expand Administrative Templates
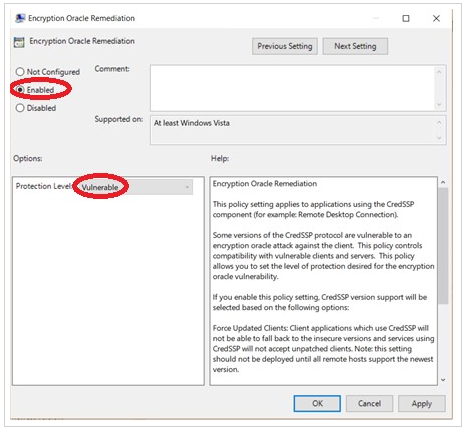
Select Enabled and change Production Level to Vulnerable
Run the command gpupdate /force to apply group policy settings. Your remote desktop connection will be working fine now.
Source : https://www.netwoven.com/2018/05/15/solved-credssp-encryption-oracle-remediation/